top of page
Insights
IAM expertise, case studies, and AI governance thinking
Practical insights from Midships engineers and architects — covering Ping Identity, Keycloak, AI governance, DevSecOps, and zero downtime delivery for regulated enterprises.
20+
Published articles
4
Content categories
Categories
Search for Midships Knowledge Base
! No Results found


eKYC (Electronic Know Your Customer)
What it is: eKYC stands for Electronic Know Your Customer , a digital process used to verify the identity of customers remotely using...

Ajit Gupta
Aug 12, 20201 min read


MFA (Multi-Factor Authentication)
What it is: MFA , or Multi-Factor Authentication , is a security mechanism that requires users to verify their identity using two or more...

Ajit Gupta
Aug 12, 20201 min read


Behavioral Biometrics
What it is: Behavioral Biometrics is an advanced Adaptive Security technique that identifies users based on unique patterns in their...

Ajit Gupta
Aug 12, 20201 min read


Zero Trust
What it is: Zero Trust is a security model that assumes no user, device, or application is inherently trustworthy, regardless of whether...

Ajit Gupta
Aug 12, 20201 min read


Ping Identity
What it is: Ping Identity is an enterprise-grade identity and access management platform that delivers solutions for CIAM , workforce...

Ajit Gupta
Aug 12, 20201 min read


CIAM (Customer Identity and Access Management)
What it is: Customer Identity and Access Management (CIAM) is a specialized branch of IAM designed to manage and secure external user...

Ajit Gupta
Aug 12, 20201 min read
Browse by topic
What we write about
Ping Identity
PingAM, PingIDM, PingDS, PingAuthorize, PingOne AIC — architecture, delivery, and operations
Keycloak and RHBK
Enterprise Keycloak delivery — HA, zero downtime, API-first, and Extended Auth Flow API
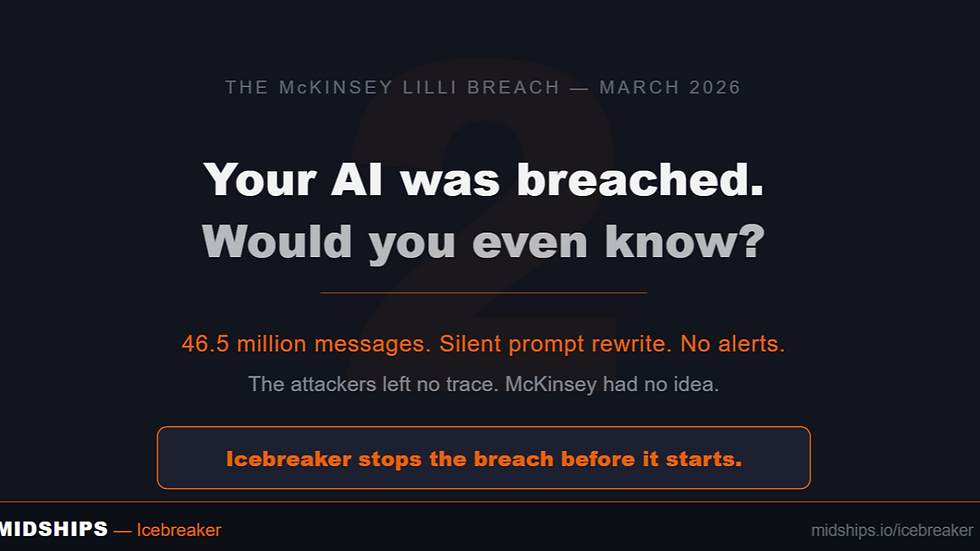
AI Governance
Icebreaker, runtime enforcement, agentic AI governance, and regulatory alignment
DevSecOps
GitOps, Kubernetes, zero downtime deployments, CI/CD pipelines, and IAM infrastructure
Stay current on IAM and AI governance
New articles, case studies, and technical guides published monthly — covering Ping Identity, Keycloak, Icebreaker, and zero downtime delivery for regulated enterprises.
bottom of page