top of page
Insights
IAM expertise, case studies, and AI governance thinking
Practical insights from Midships engineers and architects — covering Ping Identity, Keycloak, AI governance, DevSecOps, and zero downtime delivery for regulated enterprises.
20+
Published articles
4
Content categories
Categories
Search for Midships Knowledge Base
! No Results found


ForgeOps
What it is: ForgeOps is an open-source deployment framework developed by ForgeRock to automate the provisioning, configuration, and...

Ajit Gupta
Aug 13, 20201 min read


OIDC (OpenID Connect)
What it is: OpenID Connect (OIDC) is an identity layer built on top of OAuth2 that provides authentication in addition to authorization. While OAuth2 issues tokens for secure delegated access, OIDC extends it by delivering standardized ID Tokens that include verified user identity claims. It has become the de facto standard for modern IAM and CIAM , enabling federated authentication across cloud, mobile, and API-driven ecosystems. Why it matters: OIDC simplifies authentic

Ajit Gupta
Aug 12, 20201 min read


SAML
What it is: SAML is an XML-based open standard for exchanging authentication and authorization data between identity providers (IdPs)...

Ajit Gupta
Aug 12, 20201 min read


OAuth2
What it is: OAuth2 is an industry-standard authorization framework that allows applications to obtain limited access to user resources...

Ajit Gupta
Aug 12, 20201 min read


Fraud Controls
What it is: Fraud Controls are the proactive and reactive mechanisms organizations implement to detect, prevent, and mitigate consumer...

Ajit Gupta
Aug 12, 20201 min read


Identity Strategy
What it is: An Identity Strategy is a long-term plan that defines how an organization will manage, secure, and deliver seamless Identity...

Ajit Gupta
Aug 12, 20201 min read
Browse by topic
What we write about
Ping Identity
PingAM, PingIDM, PingDS, PingAuthorize, PingOne AIC — architecture, delivery, and operations
Keycloak and RHBK
Enterprise Keycloak delivery — HA, zero downtime, API-first, and Extended Auth Flow API
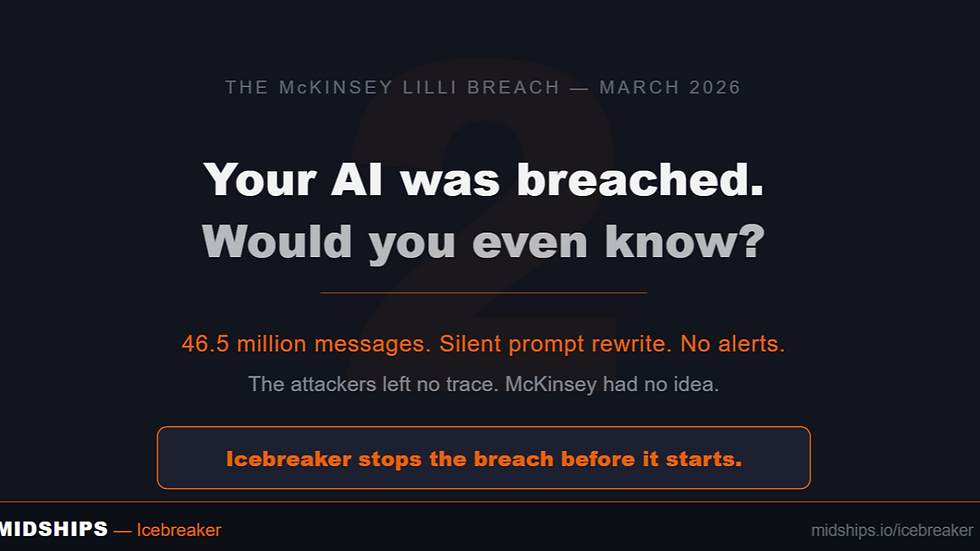
AI Governance
Icebreaker, runtime enforcement, agentic AI governance, and regulatory alignment
DevSecOps
GitOps, Kubernetes, zero downtime deployments, CI/CD pipelines, and IAM infrastructure
Stay current on IAM and AI governance
New articles, case studies, and technical guides published monthly — covering Ping Identity, Keycloak, Icebreaker, and zero downtime delivery for regulated enterprises.
bottom of page