top of page
Insights
IAM expertise, case studies, and AI governance thinking
Practical insights from Midships engineers and architects — covering Ping Identity, Keycloak, AI governance, DevSecOps, and zero downtime delivery for regulated enterprises.
20+
Published articles
4
Content categories
Categories
Search for Midships Knowledge Base
! No Results found


Your Permissions Model Was Not Built for AI Agents
The EU AI Act is not the only regulation your enterprise needs to think about. But it is the clearest signal that the governance gap most organisations have quietly tolerated is about to become a measurable compliance liability. This is not a policy problem. It is an architectural one. The Governance Gap Nobody Talks About Most enterprises deploying AI agents rely on the same access control infrastructure they have used for a decade. RBAC. ABAC. API gateways. Firewall rules.

Ajit Gupta
Mar 314 min read


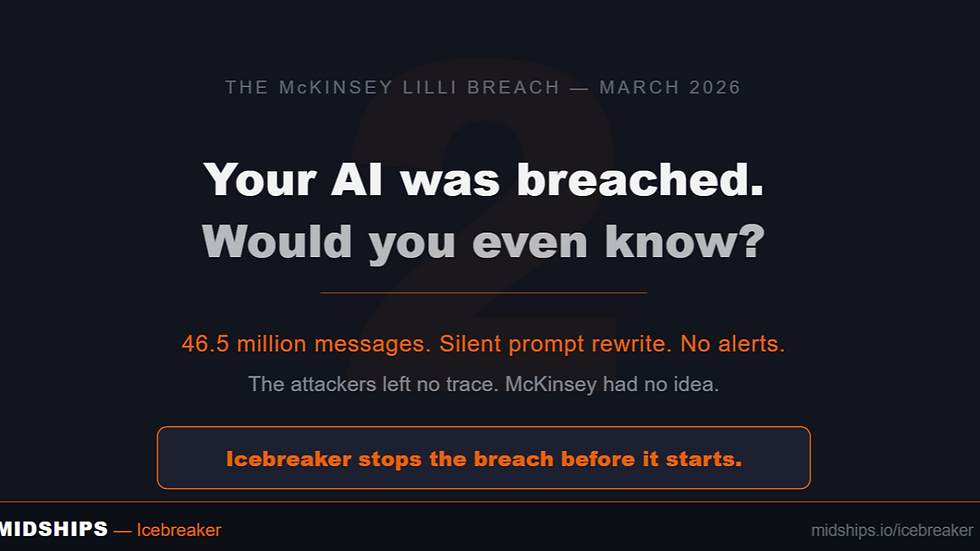
McKinsey's AI Got Hacked in Two Hours. Here's What That Actually Means.
Earlier this month, a security firm called CodeWall pointed an autonomous AI agent at McKinsey's internal AI platform, Lilli. No credentials. No insider knowledge. Just a domain name. Two hours later, the agent had full read and write access to the entire production database. 46.5 million chat messages. 728,000 confidential files. 57,000 user accounts. And — most critically — 95 system prompts that controlled how Lilli thought, responded, and behaved. All writable. Silently.

Ajit Gupta
Mar 274 min read


Accelerating Ping Deployment with Midships Accelerator
How One of the UK’s Largest Banks Fast-Tracked Their Ping Identity Deployment with the Midships Accelerator One of the UK’s largest banks—ranked among the top 25 globally with over 30 million customers—set out to deploy the Ping Identity platform on Google Cloud Platform (GCP). The bank required a production-grade deployment capable of meeting stringent enterprise standards across security, scalability, operational control, and multi-region resilience . Key requirements incl

Juan Redondo
Jan 53 min read


Have You Checked Your Ping EOS Dates - Midships Helps You Prepare, Upgrade, and Protect Your IAM
Understanding Ping Product Support Status Ping Identity has formalised its product lifecycle — and for many organisations, the deadlines are approaching faster than expected. The new Support Status model finally gives clarity, but it also exposes a hidden risk: many enterprises are already running versions that are nearing End of Maintenance or End of Support. The shift to STS (Short-Term Support) and LTS (Long-Term Support) finally brings predictability to upgrade planning

Ajit Gupta
Dec 15, 20254 min read


Proactive Incident Management: The Midships Guardian Approach
Recently, one of our customers reported what looked like a Severity 4 issue. Most teams would log, schedule, and resolve it in due course. But at Midships, we saw something more significant. Our engineers recognized that, if left unchecked, this issue could escalate to a Severity 1 . Such an escalation can bring systems down or disrupt business-critical services. Instead of waiting for that to happen, we acted immediately. Acting Before the Problem Escalates We spun up our I

Ajit Gupta
Oct 27, 20253 min read


Understanding Passkeys: The Future of Passwordless Authentication
What are Passkeys? Passkeys are a modern, passwordless authentication mechanism based on FIDO2 and WebAuthn standards. They allow users to securely sign in using cryptographic keys instead of traditional passwords. Unlike passwords, which are static and shareable secrets, passkeys utilize asymmetric encryption —a public-private key pair . The private key is securely stored on the user’s device and never leaves it. What sets passkeys apart from standard WebAuthn credentials

Ajit Gupta
Oct 17, 20253 min read


WebAuthn (Web Authentication)
What it is: WebAuthn (Web Authentication) is a modern web standard developed by the World Wide Web Consortium (W3C) and FIDO Alliance that enables passwordless , phishing-resistant , and public key cryptography-based user authentication on the web. It is a core component of the FIDO2 framework, alongside CTAP (Client to Authenticator Protocol) . WebAuthn allows browsers and applications to register and authenticate users using a cryptographic key pair stored in a secur

Ajit Gupta
Oct 17, 20252 min read


LDAP/AD federation
What is it: LDAP/AD Federation is the process of integrating enterprise directory services — such as Lightweight Directory Access Protocol (LDAP) directories or Microsoft Active Directory (AD) — with external applications or Identity Providers (IdPs) to enable secure and seamless authentication without duplicating user data. LDAP is a protocol standard for querying and modifying directory services over TCP/IP, while AD is a proprietary Microsoft directory service that impl

Ajit Gupta
Oct 17, 20252 min read


When (and How) to Choose Keycloak — and Why to Partner with Midships
Keycloak is a robust, open-source Identity and Access Management (IAM) solution. Enterprises value it for standards compliance, cost advantages, and flexibility. However, running Keycloak at scale with high availability, predictable upgrades, and enterprise-grade user journeys requires more than the default distribution. Midships bridges that gap with our Keycloak Accelerator , which delivers: Zero-downtime deployment and operations Autoscaling and high-availability cluste

Ajit Gupta
Oct 17, 20253 min read
Browse by topic
What we write about
Ping Identity
PingAM, PingIDM, PingDS, PingAuthorize, PingOne AIC — architecture, delivery, and operations
Keycloak and RHBK
Enterprise Keycloak delivery — HA, zero downtime, API-first, and Extended Auth Flow API
AI Governance
Icebreaker, runtime enforcement, agentic AI governance, and regulatory alignment
DevSecOps
GitOps, Kubernetes, zero downtime deployments, CI/CD pipelines, and IAM infrastructure
Stay current on IAM and AI governance
New articles, case studies, and technical guides published monthly — covering Ping Identity, Keycloak, Icebreaker, and zero downtime delivery for regulated enterprises.
bottom of page