top of page
Insights
IAM expertise, case studies, and AI governance thinking
Practical insights from Midships engineers and architects — covering Ping Identity, Keycloak, AI governance, DevSecOps, and zero downtime delivery for regulated enterprises.
20+
Published articles
4
Content categories
Categories
Search for Midships Knowledge Base
! No Results found


The Role of Midships in Identity Management
Identity management stands at the core of digital security for banks, insurers, gaming platforms, and fintech leaders. The challenge is...

Ajit Gupta
Sep 29, 20254 min read


Enhancing Customer Journeys with the PingOne AIC Accelerator
For teams building customer journeys, speed and consistency matter just as much as functionality. That’s where the PingOne AIC Accelerator comes in. It allows developers to create and test journeys locally in the same way they would in the cloud. This leads to faster iterations, more confidence, and less back-and-forth between environments. A Client Challenge One of our clients recently faced a roadblock: themes weren’t working in their local setup. They could build the journ
Mayank Soni
Sep 15, 20253 min read


Better PingAM Source Code Management with FACT
Customer Overview A leading gaming institution in the SEA region, leveraging the Midships Ping AIS Accelerator, sought to modernize the management of their JavaScript-based PingAM scripts, which are integral to their customer journeys. Their objective was to enhance maintainability, strengthen quality controls, and implement a more efficient code review process. This included storing source code in a readable, developer-friendly format to reduce the risk of defects reaching l

Prakhar Ananya
Sep 2, 20253 min read


The Benefits of Regularly Updating Tooling: A Technical Perspective
Abstract In modern platform engineering, tooling forms the backbone of system performance, security, and scalability. Despite this, many...

Taweh Ruhle
Aug 29, 20253 min read


Using BDD for Building User Journeys in PingOne AIC/AIS
Introduction to Behaviour-Driven Development (BDD) Behaviour-Driven Development (BDD) is a collaborative software development methodology...

Paul McKeown
Aug 5, 20254 min read


Design a Reliable PingDS Backup Strategy
Introduction Backups are essential, but they’re only valuable if they can be restored quickly and reliably. In modern infrastructure,...
Atharva Thorkar
Jul 22, 20254 min read


Where Midships Is Headed: Focused Expansion, AI Readiness, and Our Continued Commitment to Ping
As Midships continues to scale, we’ve taken time to reflect on where the market is heading—and what our customers will need from us next. Identity and Access Management (IAM) has changed. The core customer journeys and platform architectures have become increasingly commoditised. At the same time, the rise of AI is set to reshape how consulting firms operate—ours included. In response, we’re evolving. Not by pivoting away from what we do best, but by building intentionally t

Ajit Gupta
Jul 8, 20253 min read


Cross-regional Deployment including Mainland China with the Midships Ping AIS Accelerator
Introduction A valued client who was already running the Midships Ping AIS Accelerator in their Hong Kong environment, requested our...
Mayank Soni
Jun 24, 20253 min read


Identity Providers are Becoming Commodities — It's Time to Shift Focus
Identity Providers (IDPs) are becoming commoditized — and that’s a good thing. The core functions of identity management have largely...

Paul McKeown
Jun 17, 20257 min read
Browse by topic
What we write about
Ping Identity
PingAM, PingIDM, PingDS, PingAuthorize, PingOne AIC — architecture, delivery, and operations
Keycloak and RHBK
Enterprise Keycloak delivery — HA, zero downtime, API-first, and Extended Auth Flow API
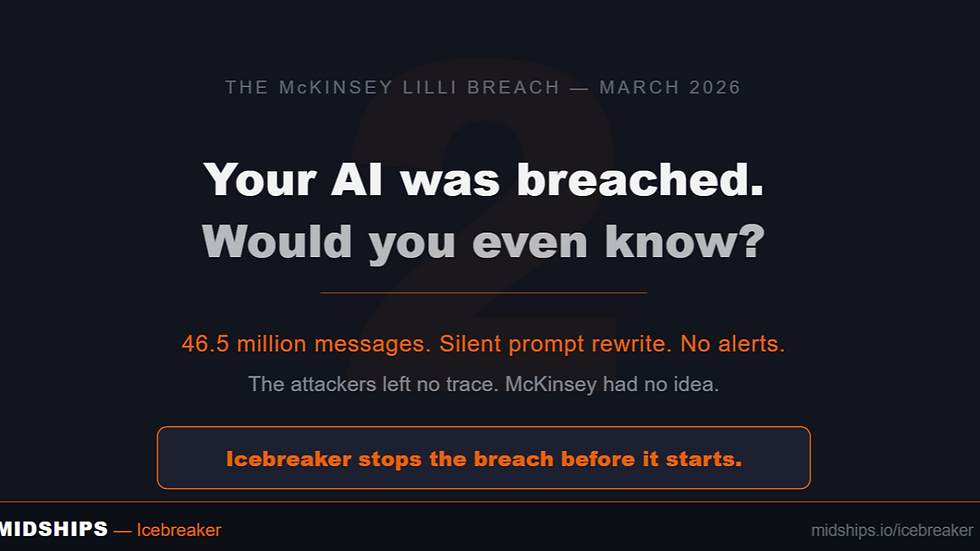
AI Governance
Icebreaker, runtime enforcement, agentic AI governance, and regulatory alignment
DevSecOps
GitOps, Kubernetes, zero downtime deployments, CI/CD pipelines, and IAM infrastructure
Stay current on IAM and AI governance
New articles, case studies, and technical guides published monthly — covering Ping Identity, Keycloak, Icebreaker, and zero downtime delivery for regulated enterprises.
bottom of page