top of page
Insights
IAM expertise, case studies, and AI governance thinking
Practical insights from Midships engineers and architects — covering Ping Identity, Keycloak, AI governance, DevSecOps, and zero downtime delivery for regulated enterprises.
20+
Published articles
4
Content categories
Categories
Search for Midships Knowledge Base
! No Results found


Infrastructure-as-Code (IaC)
What it is: Infrastructure-as-Code (IaC) is the practice of managing and provisioning IT infrastructure through machine-readable...

Ajit Gupta
Aug 12, 20201 min read


Zero Downtime IAM
What it is: Zero-Downtime IAM is the practice of designing and operating Identity and Access Management (IAM) systems to maintain...

Ajit Gupta
Aug 12, 20201 min read


IAM Journeys
What it is: IAM Journeys refer to the orchestrated authentication and authorization flows that guide users through identity-related...

Ajit Gupta
Aug 12, 20201 min read


ABAC
What it is: ABAC , or Attribute-Based Access Control , is a dynamic access management model that grants or denies permissions based on...

Ajit Gupta
Aug 12, 20201 min read


RBAC
What it is: RBAC , or Role-Based Access Control , is an access management model that grants permissions based on a user’s role within an...

Ajit Gupta
Aug 12, 20201 min read


FIDO2
FIDO2 is a password-less authentication standard developed by the FIDO Alliance and the World Wide Web Consortium (W3C). It combines the...

Ajit Gupta
Aug 12, 20201 min read
Browse by topic
What we write about
Ping Identity
PingAM, PingIDM, PingDS, PingAuthorize, PingOne AIC — architecture, delivery, and operations
Keycloak and RHBK
Enterprise Keycloak delivery — HA, zero downtime, API-first, and Extended Auth Flow API
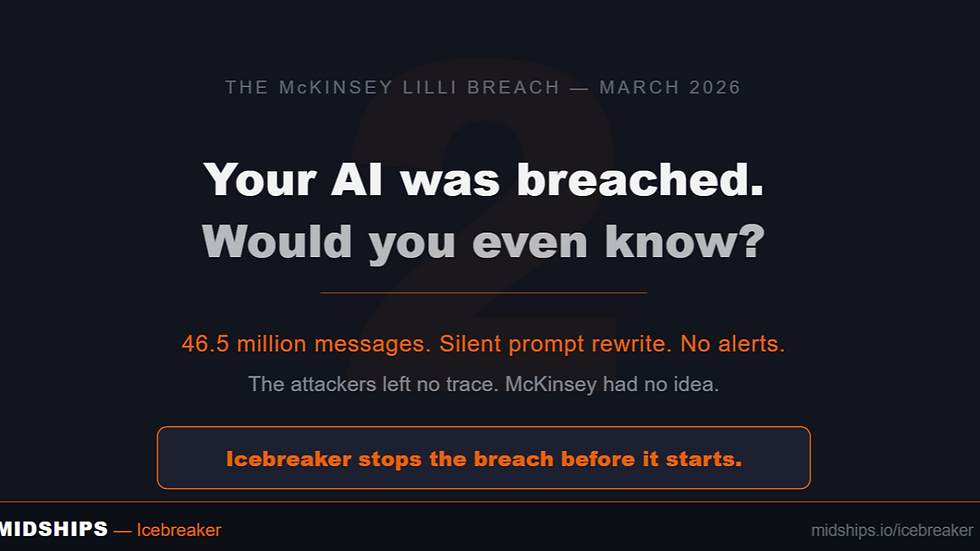
AI Governance
Icebreaker, runtime enforcement, agentic AI governance, and regulatory alignment
DevSecOps
GitOps, Kubernetes, zero downtime deployments, CI/CD pipelines, and IAM infrastructure
Stay current on IAM and AI governance
New articles, case studies, and technical guides published monthly — covering Ping Identity, Keycloak, Icebreaker, and zero downtime delivery for regulated enterprises.
bottom of page