top of page
Insights
IAM expertise, case studies, and AI governance thinking
Practical insights from Midships engineers and architects — covering Ping Identity, Keycloak, AI governance, DevSecOps, and zero downtime delivery for regulated enterprises.
20+
Published articles
4
Content categories
Categories
Search for Midships Knowledge Base
! No Results found


How Midships migrates Forgerock IDM from a Database to Forgerock DS without any disruption or interruption of service
Introduction ForgeRock’s Identity Management Solution (IDM) makes it easier for organizations to manage the identity of their members....

Midships
Mar 28, 20257 min read


Best Practices for Monitoring PingOne AIC Tenants
In today’s digital ecosystems, ensuring the health and performance of your identity platform is critical. This article explains a...

Paul McKeown
Mar 25, 20255 min read


Rapid CIAM Incident Recovery and Post-Incident Enhancements
Introduction A leading financial institution experienced a critical authentication failure when 2.7 million users were unintentionally removed from its Customer Identity and Access Management (CIAM) system. This resulted in widespread login failures, service downtime, and major disruptions to digital banking services. Midships was engaged to rapidly resolve the incident and implement proactive measures to prevent recurrence. The Challenges Mass Authentication Failures A sudde

Ravi Varma Baru
Mar 18, 20253 min read


Plan Your Cloud Journey with Midships’ Free Cloud Migration Assessment
Executive Summary Migrating from a self-managed on-premise Ping AIS environment to the cloud-hosted SaaS Ping AIC can feel like...

Paul McKeown
Mar 11, 20253 min read


Exceeding Transaction Requirements and Achieving Near-Zero RTO/RPO for a Major Asian Gaming Provider
Introduction One of the largest gaming service providers in Asia sought to modernize its Customer Identity and Access Management (CIAM) ...

Midships
Mar 3, 20253 min read
Browse by topic
What we write about
Ping Identity
PingAM, PingIDM, PingDS, PingAuthorize, PingOne AIC — architecture, delivery, and operations
Keycloak and RHBK
Enterprise Keycloak delivery — HA, zero downtime, API-first, and Extended Auth Flow API
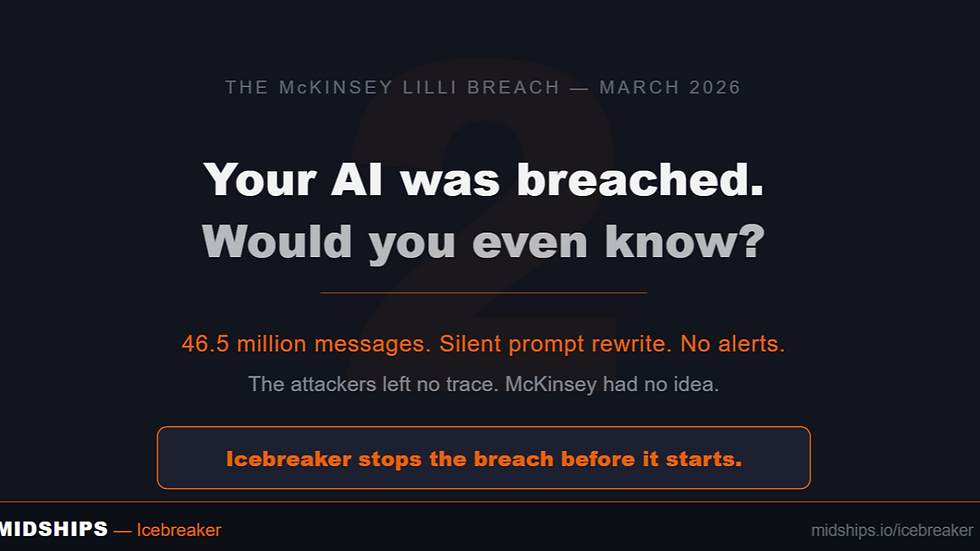
AI Governance
Icebreaker, runtime enforcement, agentic AI governance, and regulatory alignment
DevSecOps
GitOps, Kubernetes, zero downtime deployments, CI/CD pipelines, and IAM infrastructure
Stay current on IAM and AI governance
New articles, case studies, and technical guides published monthly — covering Ping Identity, Keycloak, Icebreaker, and zero downtime delivery for regulated enterprises.
bottom of page