top of page
Insights
IAM expertise, case studies, and AI governance thinking
Practical insights from Midships engineers and architects — covering Ping Identity, Keycloak, AI governance, DevSecOps, and zero downtime delivery for regulated enterprises.
20+
Published articles
4
Content categories
Categories
Search for Midships Knowledge Base
! No Results found


From Console to Compliance: Operating Keycloak as a Regulated, API-Driven Identity Platform
Abstract In regulated environments, identity systems must meet strict audit, compliance, and governance requirements. Default operational models are often insufficient, particularly when configuration changes are not traceable or reproducible. In Keycloak deployments, achieving compliance requires shifting from manual administration to an API-driven, pipeline-controlled model. This article explores how configuration management, audit pipelines, and access controls can be desi
Mayank Soni
4 days ago4 min read


Scaling Identity to Millions: Session, Token, and Cache Design in Keycloak
Primary Audience: Platform Engineers building identity infrastructure, Security architects designing authentication systems, Teams operating large-scale SaaS or financial systems. CNCF Alignment: Kubernetes, HA, Multi-RegionAbstract At scale, identity systems are defined by how sessions are managed, tokens are designed, and validation is performed. In large Keycloak deployments, these decisions directly impact performance, availability, and security. This article explores pra
Mayank Soni
May 54 min read
Browse by topic
What we write about
Ping Identity
PingAM, PingIDM, PingDS, PingAuthorize, PingOne AIC — architecture, delivery, and operations
Keycloak and RHBK
Enterprise Keycloak delivery — HA, zero downtime, API-first, and Extended Auth Flow API
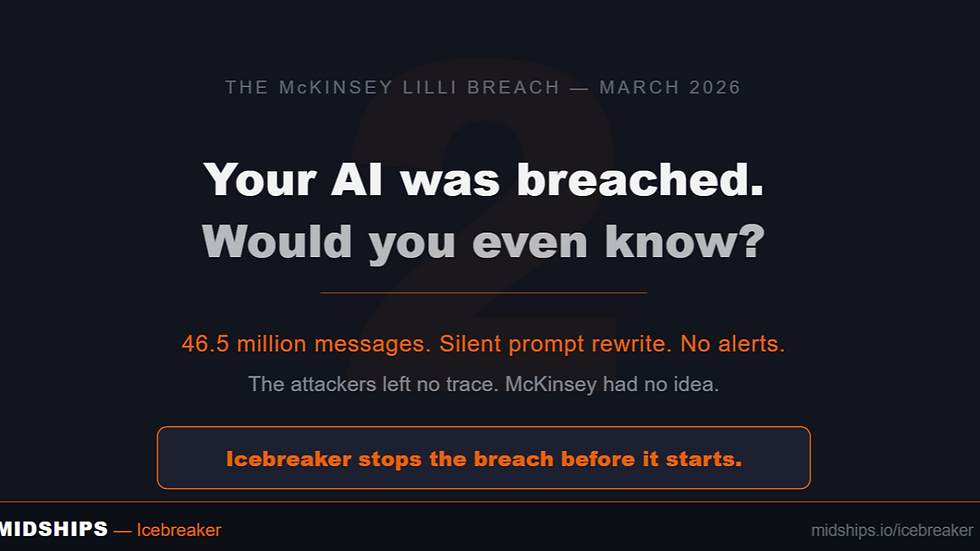
AI Governance
Icebreaker, runtime enforcement, agentic AI governance, and regulatory alignment
DevSecOps
GitOps, Kubernetes, zero downtime deployments, CI/CD pipelines, and IAM infrastructure
Stay current on IAM and AI governance
New articles, case studies, and technical guides published monthly — covering Ping Identity, Keycloak, Icebreaker, and zero downtime delivery for regulated enterprises.
bottom of page