top of page
Insights
IAM expertise, case studies, and AI governance thinking
Practical insights from Midships engineers and architects — covering Ping Identity, Keycloak, AI governance, DevSecOps, and zero downtime delivery for regulated enterprises.
20+
Published articles
4
Content categories
Categories
Search for Midships Knowledge Base
! No Results found


Proactive Incident Management: The Midships Guardian Approach
Recently, one of our customers reported what looked like a Severity 4 issue. Most teams would log, schedule, and resolve it in due course. But at Midships, we saw something more significant. Our engineers recognized that, if left unchecked, this issue could escalate to a Severity 1 . Such an escalation can bring systems down or disrupt business-critical services. Instead of waiting for that to happen, we acted immediately. Acting Before the Problem Escalates We spun up our I

Ajit Gupta
Oct 27, 20253 min read


Understanding Passkeys: The Future of Passwordless Authentication
What are Passkeys? Passkeys are a modern, passwordless authentication mechanism based on FIDO2 and WebAuthn standards. They allow users to securely sign in using cryptographic keys instead of traditional passwords. Unlike passwords, which are static and shareable secrets, passkeys utilize asymmetric encryption —a public-private key pair . The private key is securely stored on the user’s device and never leaves it. What sets passkeys apart from standard WebAuthn credentials

Ajit Gupta
Oct 17, 20253 min read


WebAuthn (Web Authentication)
What it is: WebAuthn (Web Authentication) is a modern web standard developed by the World Wide Web Consortium (W3C) and FIDO Alliance that enables passwordless , phishing-resistant , and public key cryptography-based user authentication on the web. It is a core component of the FIDO2 framework, alongside CTAP (Client to Authenticator Protocol) . WebAuthn allows browsers and applications to register and authenticate users using a cryptographic key pair stored in a secur

Ajit Gupta
Oct 17, 20252 min read


LDAP/AD federation
What is it: LDAP/AD Federation is the process of integrating enterprise directory services — such as Lightweight Directory Access Protocol (LDAP) directories or Microsoft Active Directory (AD) — with external applications or Identity Providers (IdPs) to enable secure and seamless authentication without duplicating user data. LDAP is a protocol standard for querying and modifying directory services over TCP/IP, while AD is a proprietary Microsoft directory service that impl

Ajit Gupta
Oct 17, 20252 min read


When (and How) to Choose Keycloak — and Why to Partner with Midships
Keycloak is a robust, open-source Identity and Access Management (IAM) solution. Enterprises value it for standards compliance, cost advantages, and flexibility. However, running Keycloak at scale with high availability, predictable upgrades, and enterprise-grade user journeys requires more than the default distribution. Midships bridges that gap with our Keycloak Accelerator , which delivers: Zero-downtime deployment and operations Autoscaling and high-availability cluste

Ajit Gupta
Oct 17, 20253 min read
Browse by topic
What we write about
Ping Identity
PingAM, PingIDM, PingDS, PingAuthorize, PingOne AIC — architecture, delivery, and operations
Keycloak and RHBK
Enterprise Keycloak delivery — HA, zero downtime, API-first, and Extended Auth Flow API
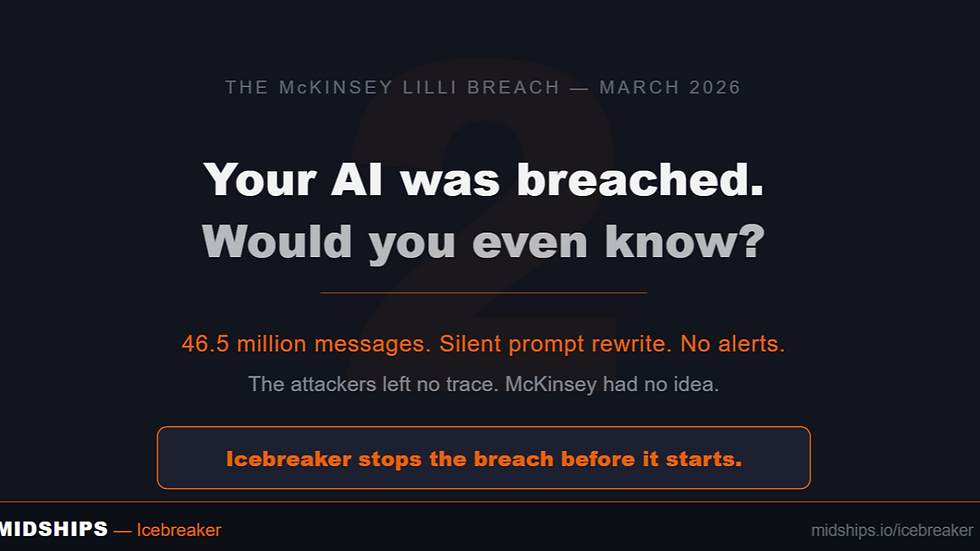
AI Governance
Icebreaker, runtime enforcement, agentic AI governance, and regulatory alignment
DevSecOps
GitOps, Kubernetes, zero downtime deployments, CI/CD pipelines, and IAM infrastructure
Stay current on IAM and AI governance
New articles, case studies, and technical guides published monthly — covering Ping Identity, Keycloak, Icebreaker, and zero downtime delivery for regulated enterprises.
bottom of page