top of page
Insights
IAM expertise, case studies, and AI governance thinking
Practical insights from Midships engineers and architects — covering Ping Identity, Keycloak, AI governance, DevSecOps, and zero downtime delivery for regulated enterprises.
20+
Published articles
4
Content categories
Categories
Search for Midships Knowledge Base
! No Results found


Cross-regional Deployment including Mainland China with the Midships Ping AIS Accelerator
Introduction A valued client who was already running the Midships Ping AIS Accelerator in their Hong Kong environment, requested our...
Mayank Soni
Jun 24, 20253 min read


Identity Providers are Becoming Commodities — It's Time to Shift Focus
Identity Providers (IDPs) are becoming commoditized — and that’s a good thing. The core functions of identity management have largely...

Paul McKeown
Jun 17, 20257 min read


Hybrid CIAM Architecture With ID Cloud
Control CIAM Resiliency with Hybrid Architecture This paper discusses Midships' design and implementation of a hybrid Customer Identity &...

Midships
Jun 13, 20255 min read


Phased Device Migration to Ping
How PingGateway Enabled a Controlled, Risk-Managed Migration to Modern Identity In a fast-moving digital identity landscape, enterprises must evolve authentication systems with minimal disruption. Midships Organization, operating globally, sought to transition from a legacy DAON deployment pattern to a modern, standards-based approach with PingAM and FIDO2 device credentials. Rather than executing a risky “big bang” switch, the team architected a phased migration strategy,

Juan Redondo
Jun 10, 20254 min read


Designing CIAM For Retail Banking: All The Core Journeys You'll Need
The Reality Check Too often, CIAM journeys are built one channel at a time. Mobile login here, web onboarding there, branch-only password resets. It works at first—until it doesn’t. As each channel evolves, it throws new demands at CIAM. You patch, you duplicate, you tech-debt your way forward. Before long, your identity layer becomes a spaghetti mess. This article is your escape route. We’re laying out a definitive list of IAM journeys and features that a retail bank CIAM

Yuxiang Lin
Jun 3, 20258 min read
Browse by topic
What we write about
Ping Identity
PingAM, PingIDM, PingDS, PingAuthorize, PingOne AIC — architecture, delivery, and operations
Keycloak and RHBK
Enterprise Keycloak delivery — HA, zero downtime, API-first, and Extended Auth Flow API
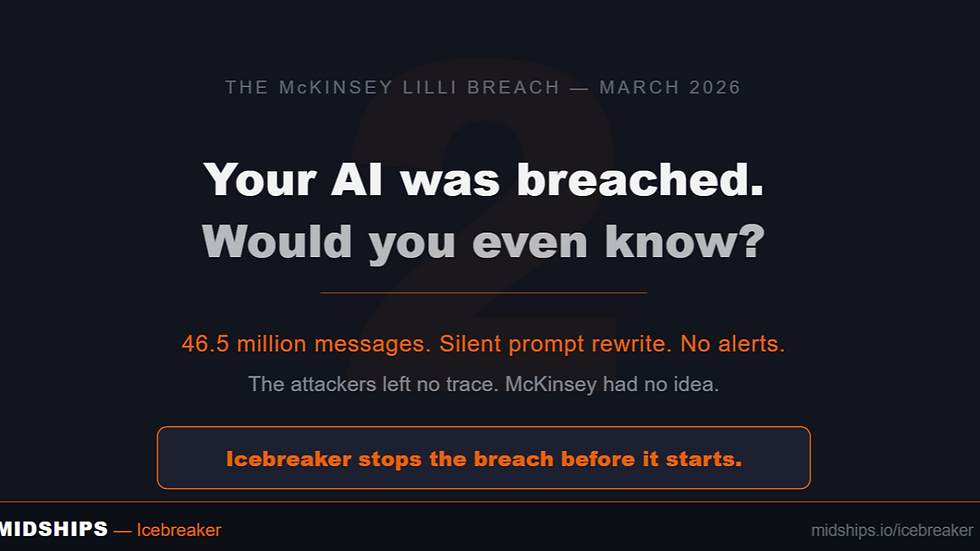
AI Governance
Icebreaker, runtime enforcement, agentic AI governance, and regulatory alignment
DevSecOps
GitOps, Kubernetes, zero downtime deployments, CI/CD pipelines, and IAM infrastructure
Stay current on IAM and AI governance
New articles, case studies, and technical guides published monthly — covering Ping Identity, Keycloak, Icebreaker, and zero downtime delivery for regulated enterprises.
bottom of page