top of page
Insights
IAM expertise, case studies, and AI governance thinking
Practical insights from Midships engineers and architects — covering Ping Identity, Keycloak, AI governance, DevSecOps, and zero downtime delivery for regulated enterprises.
20+
Published articles
4
Content categories
Categories
Search for Midships Knowledge Base
! No Results found


Best Practices for Monitoring PingOne AIC Tenants
In today’s digital ecosystems, ensuring the health and performance of your identity platform is critical. This article explains a...

Paul McKeown
Mar 25, 20255 min read


Without a strong Ops capability you will fail your customers… (Part 1)
Preface At Midships, we take pride in our originality, not merely conforming to the norm. Our dedicated team devotes considerable time to...

Midships
Dec 29, 20243 min read


Embracing Hybrid Architectures for Ping CIAM Platforms
Preface At Midships, inquiries about Hybrid Architectures are common, and although we possess whitepapers on the subject, creating a...

Midships
Dec 7, 20242 min read


Optimise Your Directory Service
Keep the User Store Clean Over time, dormant user profiles and historical device profiles can accumulate in the user store ( directory...

Midships
Jun 13, 20242 min read


Agent Verification: A low cost and simple approach to battle Social Engineering!
Executive Summary This paper outlines Midships’ approach to combat social engineering fraud, focusing on the scenario of phone call-based...

Midships
May 21, 20245 min read


SCA using Dependency Track (with AWS CDK Deployment Template)
Introduction Software Composition Analysis (SCA) is an essential activity in the development of software or infrastructure. It helps...

Midships
Apr 18, 20249 min read
Browse by topic
What we write about
Ping Identity
PingAM, PingIDM, PingDS, PingAuthorize, PingOne AIC — architecture, delivery, and operations
Keycloak and RHBK
Enterprise Keycloak delivery — HA, zero downtime, API-first, and Extended Auth Flow API
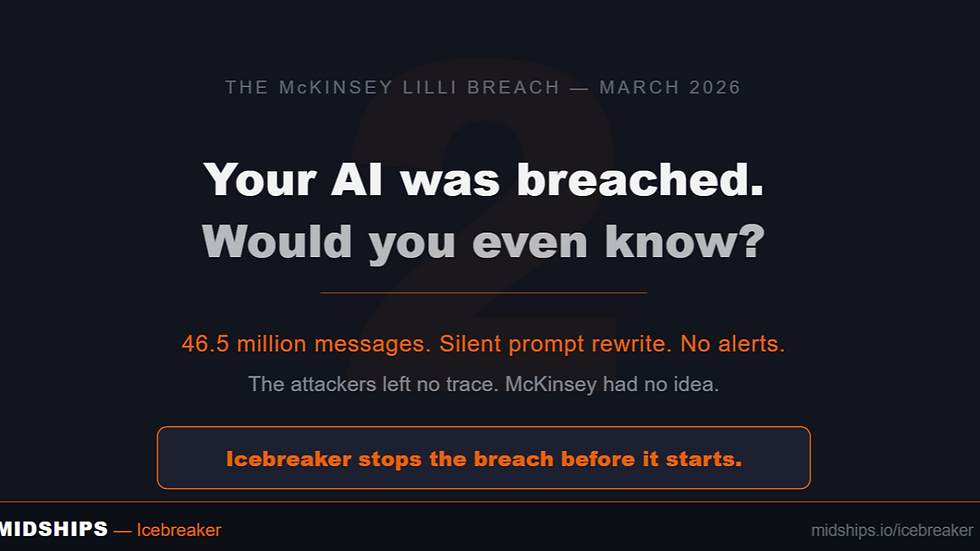
AI Governance
Icebreaker, runtime enforcement, agentic AI governance, and regulatory alignment
DevSecOps
GitOps, Kubernetes, zero downtime deployments, CI/CD pipelines, and IAM infrastructure
Stay current on IAM and AI governance
New articles, case studies, and technical guides published monthly — covering Ping Identity, Keycloak, Icebreaker, and zero downtime delivery for regulated enterprises.
bottom of page